Predict. Detect.
Annihilate.
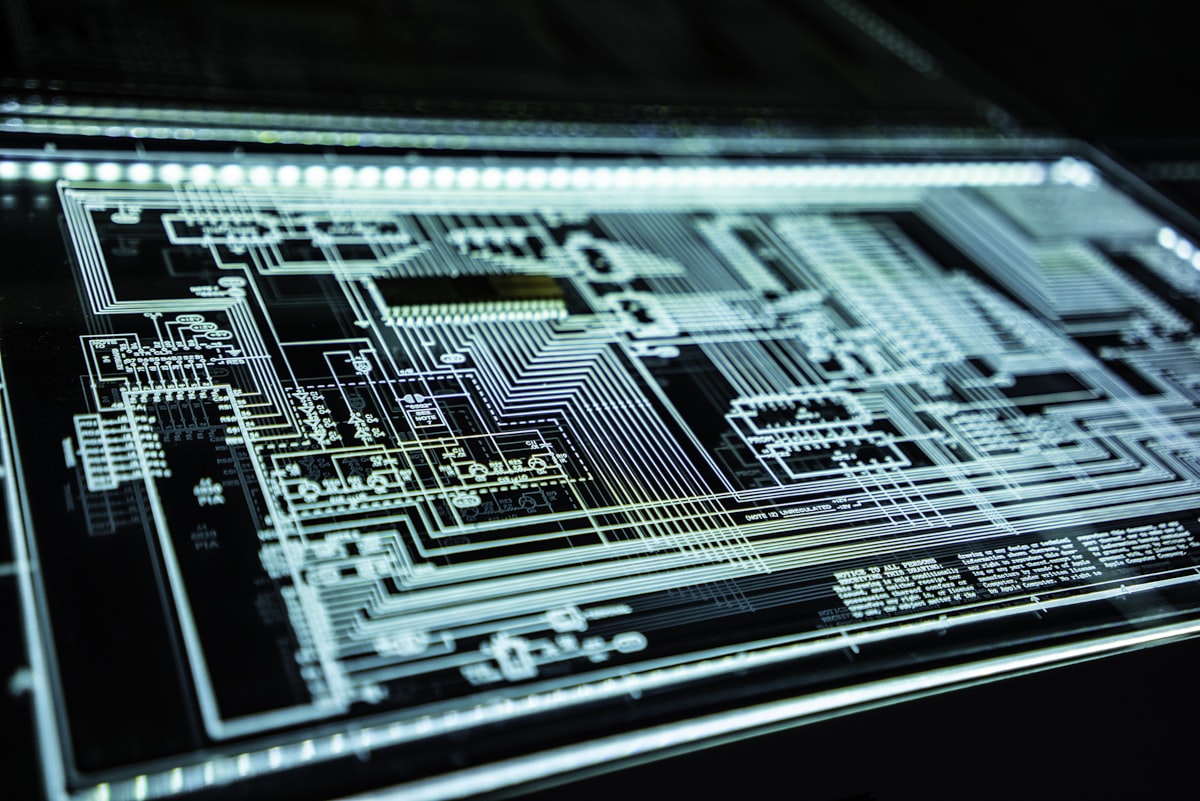
AI-Powered Threat Intelligence & Zero-Day Defense
Our AI-driven security operations center processes over 50 million events daily, combining advanced threat hunting, behavioral analytics, and autonomous response to neutralize adversaries before they strike. From ransomware defense to adversarial AI protection, we architect the impenetrable.