Why Visionleap
Not Just Protection.
Dominance.
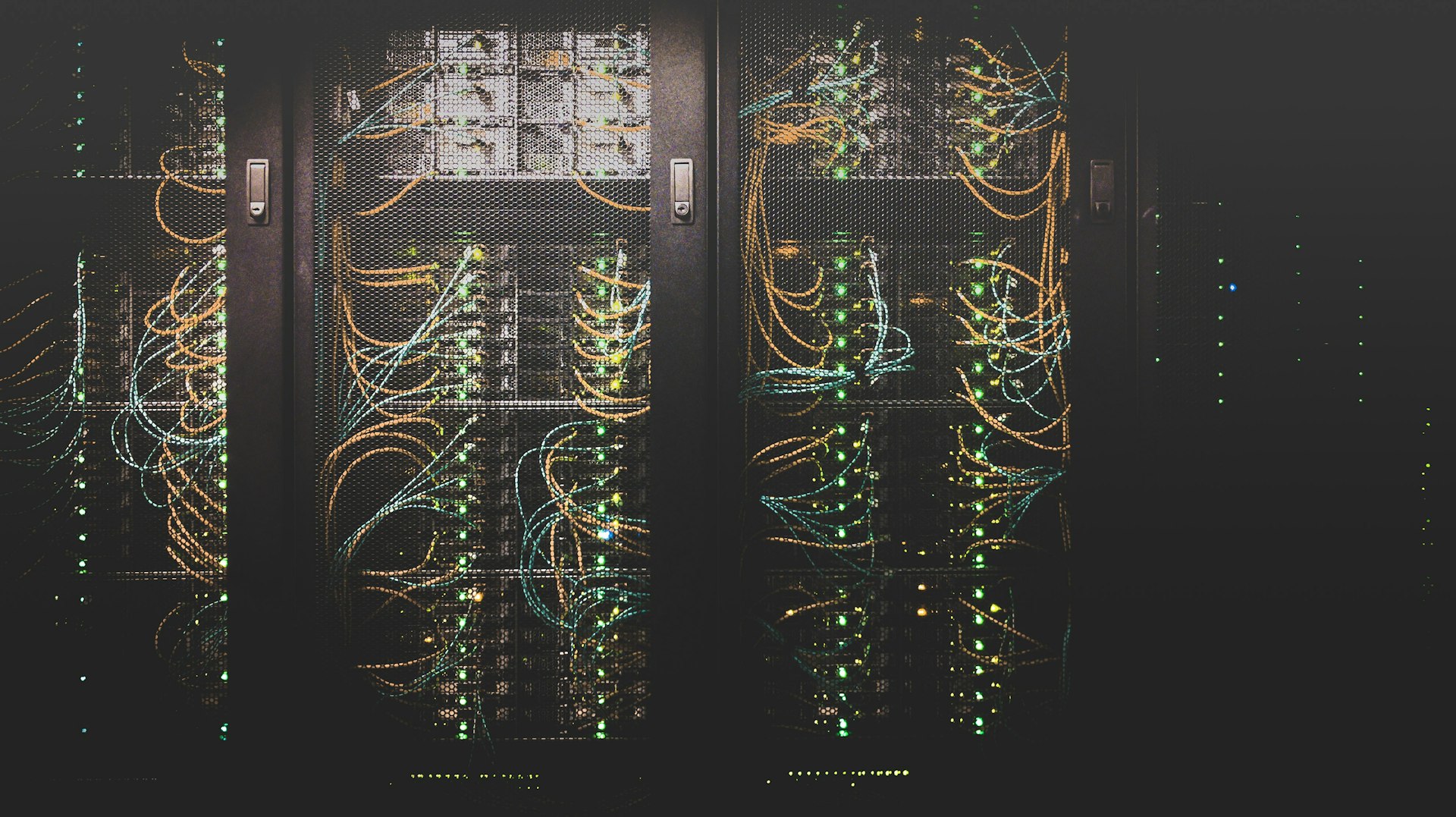
In an era of escalating AI-powered attacks, state-sponsored threats, and quantum computing breakthroughs, conventional security is obsolete. We engineer adaptive defense systems that don't just respond to threats — they predict, prevent, and annihilate them.
Excellence